Vidar’s Game: Infostealer in a Music App Costume with Lumma’s Touch

I recently came across a malware sample that had me second-guessing: was it Lumma, or the notorious Vidar stealer? The lines between these malware families are increasingly blurred, but a deeper dive revealed the sample’s true identity: a potent Vidar Stealer, version 14.9.
Despite the name game, its mission is brutally clear: to execute a multi-stage heist and exfiltrate credentials, crypto wallets, and sensitive data. This particular operation is meticulously tracked by its operators using campaign IDs like reeqc and 5109e55a90691a349041640c084efcd8.
It all starts with a clever ruse — a fake music app installer. Here’s a breakdown of how Vidar pulls off its sophisticated attack right under the radar.
VIDAR is a C++-based data stealer designed to extract sensitive information from multiple web browsers, cryptocurrency wallets, chat applications, the Authy two-factor authentication app, and various other software. The harvested data is compressed before being transmitted via HTTP to a remote command-and-control server.
Stage 1: The Trojan Horse
Like any good heist, it begins with a convincing entry plan. The victim, wanting to install the popular music app, downloads and runs a file named SpotifyInstaller.exe. This file is Vidar’s Trojan horse. Instead of music, it delivers a malicious payload.
(a878403de3e5bb45ac3683a1fe2461616c5b2598917c70e2cdf32319f7f27bb1)
Immediately upon execution, the installer’s true purpose unfolds. It acts as a dropper, placing a second executable file, chondriomererecce.exe, into the C:\Users\Public\Documents directory. This location is often less scrutinized by both users and security tools. To cover its tracks and make analysis harder, it then launches this new file using a detached command prompt process:
cmd /c start %PUBLIC%\Documents\chondriomererecce[.]exeThis hand-off is the first step in obfuscating the attack chain. The initial installer has done its job, and the secondary payload now takes over.
Stage 2: Hiding in Plain Sight with MSBuild
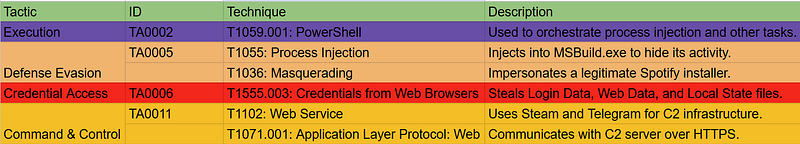
Once active, Vidar’s primary concern is stealth. It can’t operate for long as an unknown, suspicious process. To solve this, it employs a sophisticated “living off the land” technique: process injection into a legitimate Microsoft tool.
In this variant, the target is MSBuild.exe. This is the Microsoft Build Engine, a core, trusted component of Windows used by developers to compile code. By injecting its malicious code into this signed and reputable process (MITRE ATT&CK T1055), Vidar effectively wraps itself in a cloak of legitimacy.
The injection is orchestrated by PowerShell, which acts as a bridge to transfer the malicious logic into the memory of MSBuild.exe. Now, any hostile activity, scanning files, making network connections—appears to originate from the trusted MSBuild.exe, fooling security products. Vidar has successfully established a stealthy internal slave to carry out its bidding.
Stage 3: The Data Heist
With its stealthy operator in place, Vidar begins the main phase of its mission: theft. The compromised MSBuild.exe process is directed to navigate the file system and hunt for a treasure trove of sensitive information stored by web browsers. It specifically targets the Google Chrome user profile folder, exfiltrating critical files:
Login Data: A database containing all saved usernames and passwords.Web Data: A file storing autofill data, including credit card numbers and addresses.Local State: The most critical file, containing the unique encryption key needed to unlock the passwords and data in the other stolen files.
With these three files, the attackers have everything they need to impersonate the victim across countless websites, from social media and email to online banking and corporate portals.
Stage 4: Phoning Home with the Loot
After gathering the data, Vidar must exfiltrate it back to its operators. Its Command and Control (C2) infrastructure is designed for resilience and stealth, using multiple layers of indirection to make tracing and blocking incredibly difficult.
- Initial Redirection: The process begins by leveraging legitimate public web services. This sample was configured to first check a specific Steam community profile to find its next instruction. By fetching this page, it retrieves the next step in the chain. A decoded configuration string reveals how the malware identifies itself:
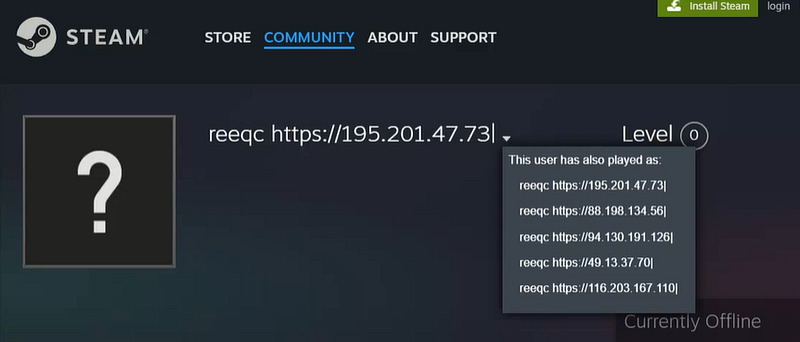
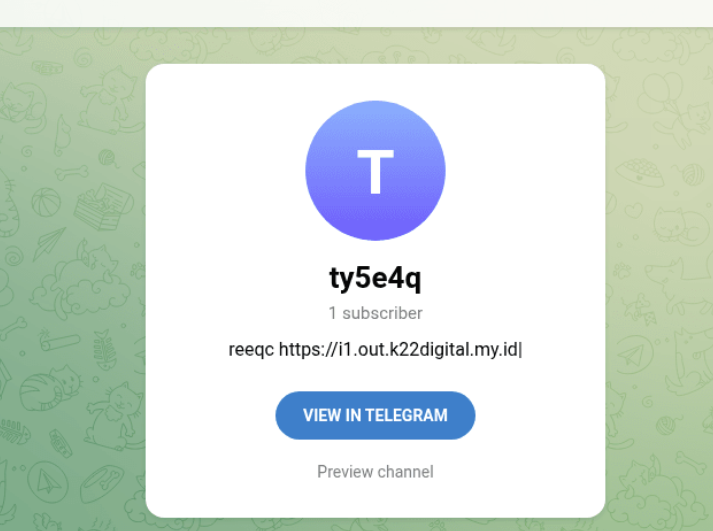
{"C2 url": "hxxps[:]//steamcommunity[.]com/profiles/76561199884432485", "Botnet": "reeqc"}- Secondary Hop (Dead Drop): This redirection leads to another seemingly legitimate service. In this case, the Telegram channel
t.me/ty5e4qwas used not as the final C2, but as a dead drop pointing to another link:hxxps[:]//s3.cdn.k22digital.my[.]id. Using a Content Delivery Network (CDN) link is a clever tactic to host malicious payloads, as CDN traffic is high-volume and often trusted, making it difficult to block outright.
- Final C2: The final C2 server address, such as the domain
*.payoopoint[.]lk, is then retrieved from the resource hosted on this CDN.
This entire multi-hop process, from infection to exfiltration, is tracked by the attackers using unique campaign identifiers like reeqc, allowing them to measure the success of their various distribution methods and making the C2 infrastructure significantly more challenging for defenders to dismantle.
MITRE ATT&CK Framework:
Conclusion
So, the takeaway is pretty clear. The Vidar Stealer is a serious tool for stealing your info. It’s clever, mixing a simple fake installer trick with the more advanced technique of hiding inside a normal Windows process like MSBuild.exe. The fact that it uses everyday services like Steam and Telegram to call home shows these threats are constantly adapting.
This all just proves that good security isn’t just about having antivirus; it’s also about being careful and knowing what you’re running on your system. For organizations, this is a stark reminder that the entire attack, from initial execution to data exfiltration, can take less than two minutes, making EDR solutions and continuous monitoring non-negotiable for rapid detection and response
Indicators:
ThreatFox: https://threatfox.abuse.ch/browse/malware/win.vidar/
0dadd34c769fbddd20dd46ab6b5ef6007d3f0d4e7c88388f0665026b5106ed9d
aeb2bc156e63397d612e2f11a08d64b7df980bc73e166bf2011f25ce7c331283
891a36d2f68d8388c786099c9292d9c37321ba8d76ebe8322e7b624d33160436
2ba6e2f5de561c10dcbddee0ccc2afbeca35bf6a0cb412063d1a23ffc071a954
b25fe4a27296158ab5dd0bbb14fc16dbd70adb1997255a6d3ca32f9cf502de13
83876db6a537ae34e7ba3c36a97b2502daa896b9202e6ea2eb237b52cb6a41b0