The Fox and the RAT: A Sophisticated Cyber Operation in South Asia

By now, many security analysts have probably seen ValleyRAT, especially since mid-July 2025. The campaign seems to be spreading quickly, and the attackers have spread out many different variant of the malware, trying to reach as many targets as possible.
What is ValleyRAT?
ValleyRAT is a remote access trojan that is linked to the Silverfox group. This malware works like a backdoor, letting attackers control infected computers, steal information, and stay hidden on the system for a long time. Looking at samples of ValleyRAT shows that it has features like stopping other processes, avoiding detection, and using different modules. These features show it is meant for long-term spying, not random attacks, demonstrating the Silverfox group’s careful and flexible approach.
While collecting samples, I noticed multiple behaviors, largely because some of the targets were specifically attacked by the SilverFox group, which uses a more sophisticated attack pattern. However, we will focus on a sample that takes a simpler and more unique approach to achieving its goal. Most of the post-infection activity is carried out through Winos 4.0, and in some instances, the Microsoft Dr. Watson User-Agent (MSDW) was also observed.

Silverfox: Beyond the Phishing Campaigns
Based on samples gathered from VirusTotal and Malware Bazaar, it appears that the threat actors behind Silverfox have also circulated ValleyRAT using SEO poisoning campaigns. Users are tricked into visiting seemingly legitimate websites and downloading malicious files, which are often trojanized versions of popular software.
- Tencent application, QQHong application
- LINE application
- LetsVPN , KL VPN,BJ VPN
- LD Player, Music applications,
- Just-In-Time (JIT) debugger
- Fake Chrome Setup, and Chat Apps
- Snip Setup, Coin Win, VNC Tools,
- Random Gaming softwares
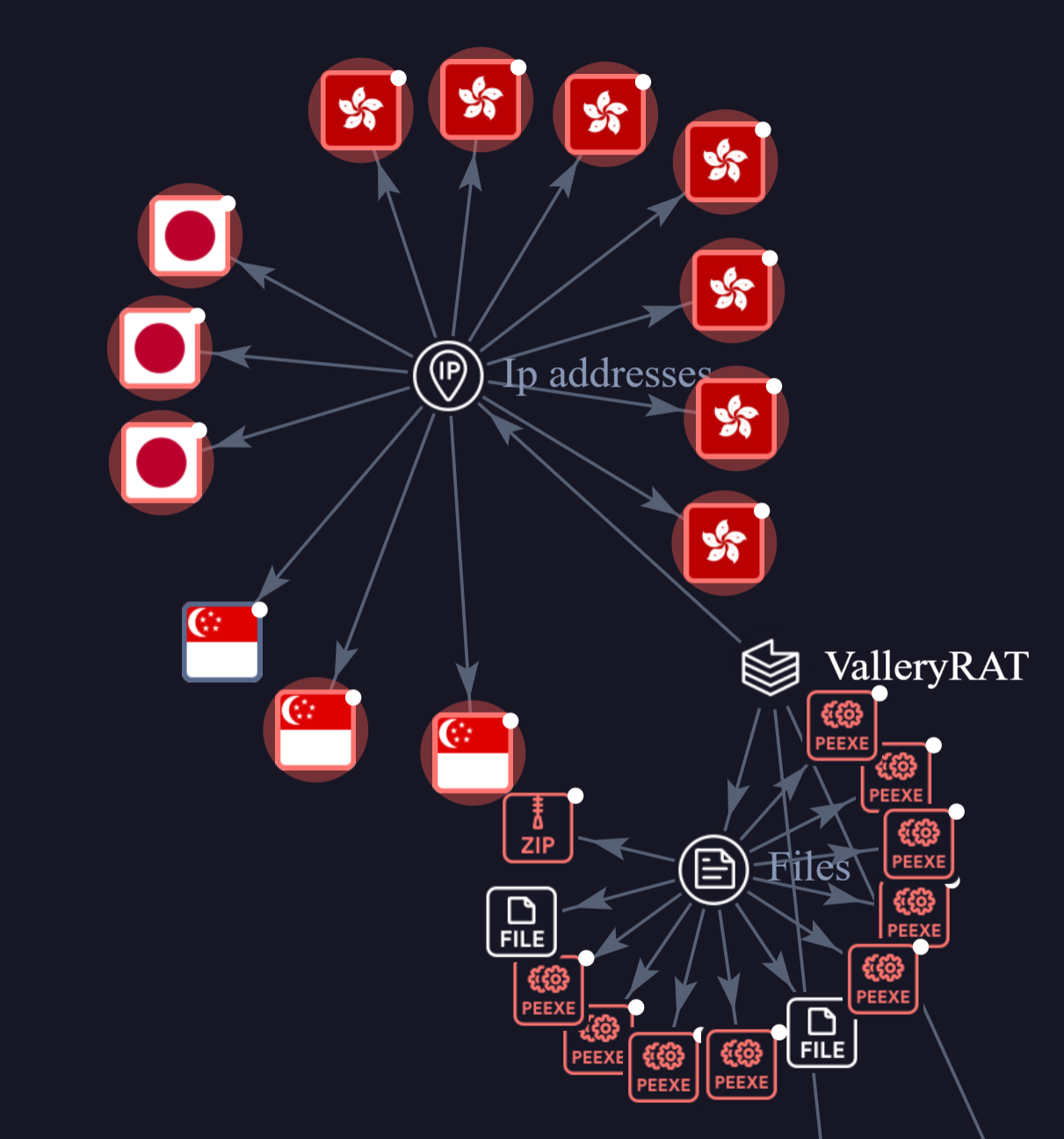
Most of the payloads are delivered through Tencent Cloud CDN and Alibaba Cloud's Object Storage Service (OSS), and their command-and-control (C2) infrastructure is mainly hosted on IP addresses located in Hong Kong, Japan, and Singapore.
The intent behind this does not appear to be monetization; instead, it seems focused on intelligence gathering and maintaining a presence on the computer to support future objectives.
Case Study: Tracing ValleyRAT – The September 3, 2025.exe Infection Chain
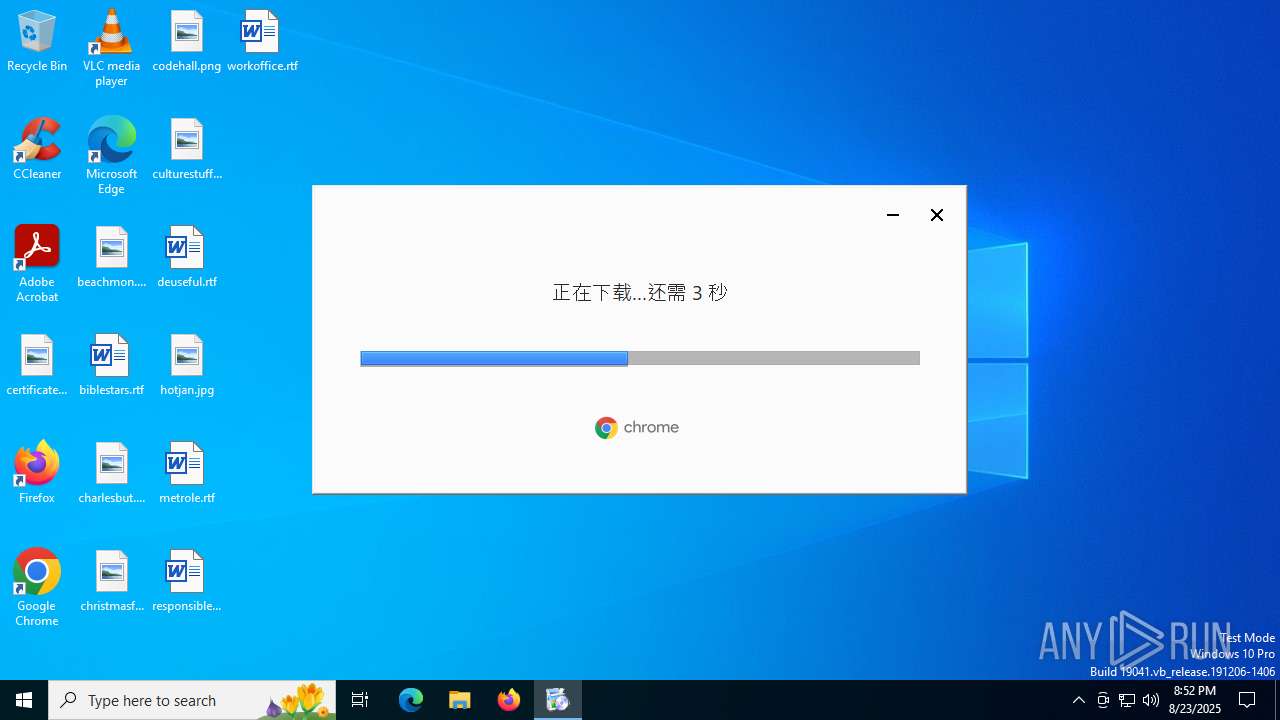
Disguised as a harmless document, the September 3, 2025.exe (VsJITDebugger.exe - Visual Studio Just-In-Time Debugger) file carries out a sophisticated intrusion characteristic of a well-developed ValleyRAT campaign. The analysis points to a careful and deliberate attacker who values stealth and evasion at every stage of the attack.
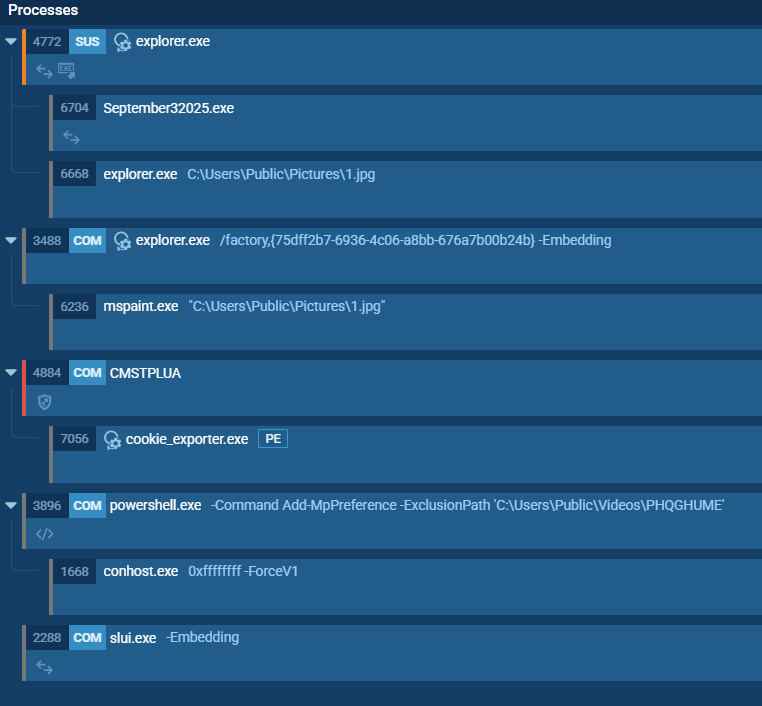
The attack starts with a familiar social engineering trick, using a deceptive filename to convince the victim to run the file. Once executed, the malware doesn’t reveal its true purpose right away. Instead, it quietly works to weaken the system’s defenses. It uses advanced methods like direct system calls and evasive API chains to stay hidden from standard EDR tools and to avoid detection in sandbox environments. A key tactic involves leveraging the CMSTP technique to bypass User Account Control (UAC), allowing the malware to gain elevated privileges without triggering any user alerts.
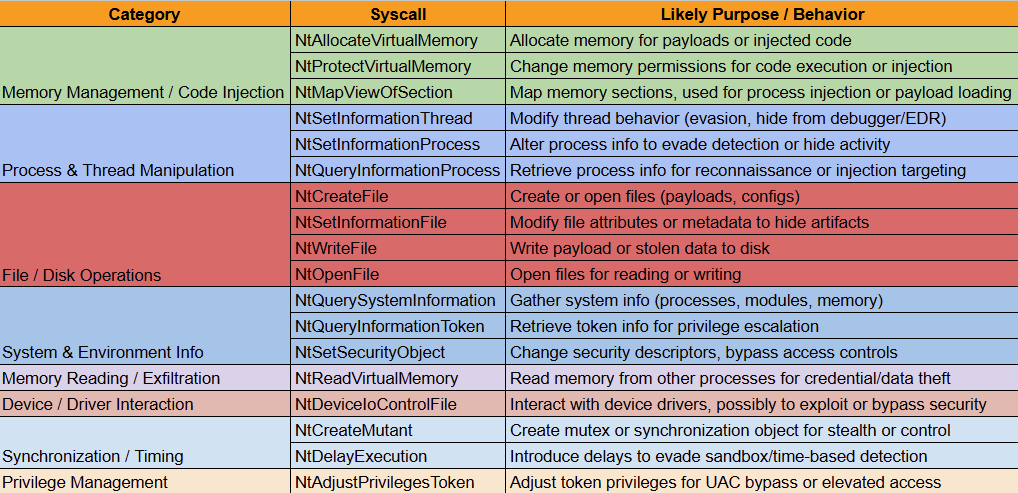
The trojanized file executes numerous syscalls, ValleyRAT uses to carry out its stealthy operations and maintain persistence. Each syscall type plays a specific role in the attack chain, enabling the malware to operate under the radar of security tools while achieving its malicious goals. The breakdown is as follows:
After weakening the system’s defenses, the malware takes an extra step to prepare for persistence. It runs a PowerShell command to add its staging folder C:\Users\Public\Videos\PHQGHUME\, to the Windows Defender exclusion list. By doing this, it creates a safe zone on the system where its main components can run without being scanned or blocked.

The next stage of the attack showcases a classic example of modern process injection. Instead of running as a visible malicious process, the malware takes a stealthier route by injecting itself into the legitimate explorer.exe process. It even hooks into ntdll.dll to hijack a key part of the Windows interface. From this trusted position, it delivers its main payload, cookie_exporter.exe, into the directory it had already excluded from Windows Defender scans.
Once executed, the secondary payload, cookie_exporter.exe, embeds itself into a legitimate svchost.exe process. By operating from within this trusted process, the malware conceals its actions among normal system activity, making it highly challenging for security tools to spot.
valley_rat_injections:
- source: "C:\\Users\\user\\Desktop\\September 3, 2025.exe"
target: "C:\\Windows\\explorer.exe"
section_loaded: null
protection: "execute and read"
- source: "C:\\Users\\user\\Desktop\\September 3, 2025.exe"
target: "C:\\Windows\\explorer.exe"
section_loaded: null
protection: "read write"
- source: "C:\\Users\\Public\\Videos\\PHQGHUME\\cookie_exporter.exe"
target: "C:\\Windows\\System32\\svchost.exe"
section_loaded: null
protection: "execute and read"
- source: "C:\\Users\\Public\\Videos\\PHQGHUME\\cookie_exporter.exe"
target: "C:\\Windows\\System32\\svchost.exe"
section_loaded: null
protection: "read write"
- source: "C:\\Windows\\System32\\svchost.exe"
target: "C:\\Windows\\System32\\sihost.exe"
section_loaded: null
protection: "execute and read"
Process Injection
Post all these activities, the malware sets up its Command and Control (C2) channel. The network activity matches the signature of the Winos4.0 framework, with the infected system initially exchanging login messages with 27.124.43[.]13. The attacker seems to be probing for open connections or creating backup paths by connecting to multiple ports on the C2 server. Ultimately, it establishes an encrypted connection to 47.79.48[.]27 over port 443, masking its communications and data transfers.
Finally, after the C2 channel is active, the purpose of cookie_exporter.exe becomes apparent: it collects browser cookies and other authentication data. This sensitive information is then sent to the attacker over the encrypted connection, giving them access to the victim’s online accounts and digital resources.
In conclusion, this ValleyRAT sample is far from a simple smash-and-grab malware. It is a sophisticated and mature implant, showing a thorough understanding of modern security tools and how to bypass them. Its careful blend of anti-analysis techniques, defense evasion, and persistent capabilities makes it a significant threat to systems, particularly in South Asia.
Few other interesting samples:

Known Indicators
Indicator Type Indicator
IP 103[.]243[.]26[.]240
IP 130[.]250[.]191[.]52
IP 137[.]220[.]153[.]69
IP 137[.]220[.]153[.]90
IP 137[.]220[.]154[.]46
IP 14[.]128[.]63[.]155
IP 143[.]92[.]37[.]143
IP 148[.]66[.]11[.]10
IP 23[.]249[.]28[.]223
IP 27[.]124[.]38[.]6
IP 38[.]14[.]248[.]131
IP 43[.]198[.]22[.]232
IP 45[.]204[.]197[.]202
IP 45[.]204[.]215[.]15
IP 8[.]210[.]88[.]96
FILE 265735e522bc53a016b41c94ce8e3386015022d9ade19e8a91b7ce4010f2ba4b
FILE 74de60385b0ee246f7ad7f52a974830f2c22ae95293d5002429155f95054a3eb
FILE 769349ff215d22e97adc0edbb1173b84fb139ba97b36cd7edf81e562e9c69816
FILE 7eb711f26136b75f14e980fd0a0611531e5f45293a8088926e8c7aacef8bcdf6
FILE 8ff7bf8dfda2d9edd97a9793a4cc24970b7ddb6661e545b159dbdaaccd029299
FILE bf745a2d1127d21d4f50f64e9b0a58b112c40ca359f040dc864f2ce940b487c9
FILE cf368705c5cd6cd0f824d5ca8b5f187488fbd4d436a93a60f57f8cfd6a004398
FILE db53b8facfc960e2654dd0d69f34f9a8c8f2d4344addde1d41cf3f84ef83dc5a
FILE e986a355dbb1dbafc12556722ea63671478defb5887b7bfdb328b8373cf6f070
FILE ee373e7b07e409927a53edc6c2e929c49de80f34adfcfc9d0d8be96ba2598d52
FILE 6d53d3600c9263c6966565d647a6ab1935b9140d2216e70d81c3b88c7adc9792
FILE b86cfbb1c101ebf0555942713b3e08add02643c54e16856e348ad41070346d72
FILE cf368705c5cd6cd0f824d5ca8b5f187488fbd4d436a93a60f57f8cfd6a004398)
DOMAIN knoeyyrt[.]com
DOMAIN x[.]zbj888uul[.]com
DOMAIN symptomatic[.]quest