A Security Analyst’s Guide to Security Identifiers (SIDs)
As a security analyst, you’re constantly on the lookout for the tell-tale signs of malicious activity. In the world of Windows security, one of the most fundamental and often overlooked artifacts is the Security Identifier (SID).

Understanding SIDs is not just academic; it’s a practical skill that can significantly enhance your ability to detect, investigate, and respond to security incidents. This article will break down what SIDs are, how they are structured, and most importantly, how you can leverage them in your daily investigations.
What is a Security Identifier (SID)?
A Security Identifier (SID) is a unique and constant string of characters that Windows uses to identify a security principal. A “security principal” can be anything that can be authenticated by the operating system, including:
- A user account
- A group of users
- A computer account
- A service
Think of a SID as a digital fingerprint for every user, group, and computer on a Windows network. Even if a user changes their name, their SID remains the same. This makes SIDs an incredibly reliable way to track activity and permissions.
Strucuture of a SID
At first glance, a SID might look like a random string of numbers, but it has a very specific and logical structure.
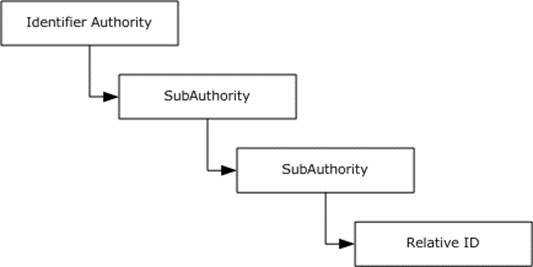
Let’s break it down using an example: S-1–5–21–1004336348–1177238915–682003330–500
S: This is the revision level, which indicates that it's a SID.1: This is the revision number of the SID specification.5: This is the identifier authority value, which specifies the authority that issued the SID.5represents the NT Authority.21-1004336348-1177238915-682003330: These are the subauthority values, which include the domain identifier. This part is unique to a specific domain or local machine.500: This is the Relative Identifier (RID). The RID is what uniquely identifies an account or group within a domain. A RID of500is always reserved for the built-in Administrator account.
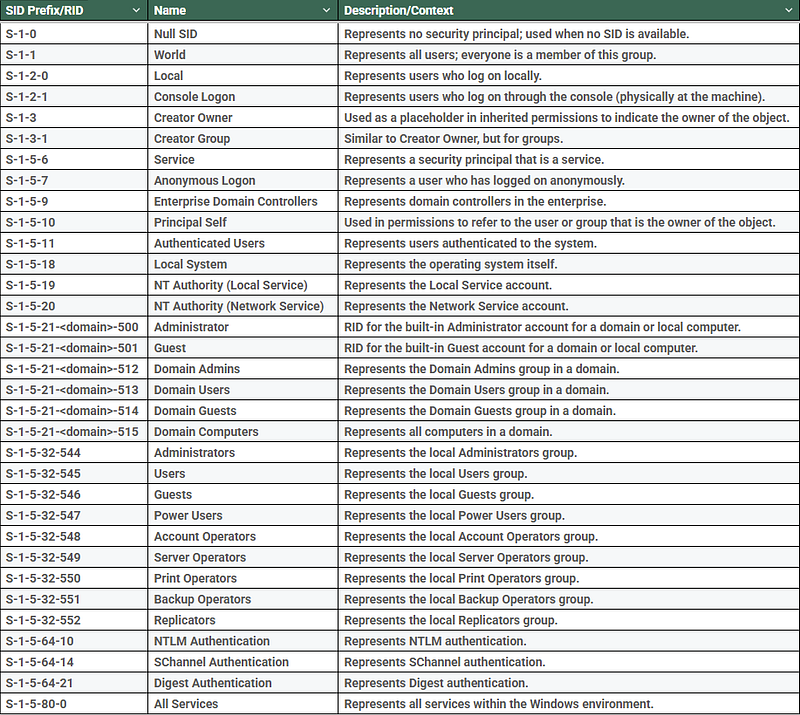
Well-Known SIDs: The Usual Suspects
Windows has a set of “well-known SIDs” that are predefined and consistent across all Windows systems. As a security analyst, you should be familiar with these, as they can help you quickly identify the context of an event.
Here are some of the most important ones:
The Analyst’s Workflow for SID Investigation
To effectively use SIDs during an investigation, a security analyst can follow a structured workflow. The flowchart below illustrates the decision-making process, from the initial alert to the final resolution. This process helps ensure that SIDs are properly identified, analyzed for context, and used to determine if an activity is malicious.
SIDs in Action: A Practical Guide for Security Analysts
Now for the most important part: how can you use this knowledge in your investigations?
- Identifying User and Group Privileges :
When you’re analyzing logs, you’ll often see SIDs instead of usernames. By understanding what the SIDs represent, you can quickly determine the privilege level of the account involved. For example, if you see activity associated with the SID ending in -500 (Administrator), you know it’s a high-privilege account and should scrutinize its activity closely.
- Tracking Lateral Movement
Attackers often try to move laterally across a network by compromising one account and then using it to access other systems. By tracking SIDs in event logs (like Windows Security Event ID 4624 for successful logons), you can follow an attacker’s trail, even if they are trying to hide their tracks by using different usernames.
- Detecting Anomalous Behavior
Your understanding of SIDs can help you spot anomalies.
For instance: Unusual Group Memberships: If you see a SID for a standard user account added to a privileged group like Domain Admins (SID ending in -512), it’s a major red flag.
Suspicious Service Accounts: If a service account (e.g., S-1–5–20 for Network Service) is performing actions typically associated with a user account, it could indicate a compromised service.
Anomalous Logon Types: Seeing a SID associated with a local logon (S-1–2–0) for an account that should only be logging in remotely could be a sign of a security breach.
Conclusion
Security Identifiers are more than just a technical detail of the Windows operating system; they are a vital source of information for any security analyst. By taking the time to understand SIDs, you can gain a deeper insight into the events on your network, enabling you to conduct more effective and efficient investigations. So, the next time you see a long string of numbers in your logs, don’t just see it as noise — see it as a clue.
Good references:


#SID #Security Identifer #User Accounts